August 29th, 2013
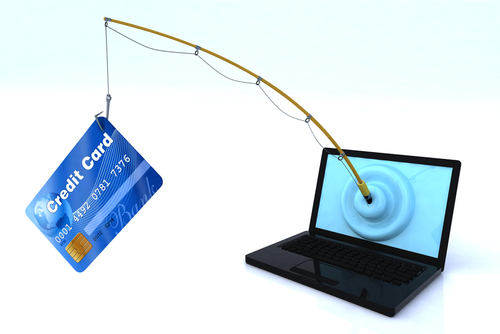
The instances of phishing attacks is on an aggressive rise. Over the past 12-months, the number of users who have experienced a phishing attack has risen 87-percent, from 19.9-million to 37.3-million.
During that time, there have also been multiple high-profile attacks, whose victims have included Twitter and the New York Times. Anyone can be a victim to a phishing attack and the rise in victims seems to indicate an increase in the number of threats online. It also suggests that more users need to understand the risks and how to avoid them.
Brian Clark Howard delved into this topic for National Geographic to help educate users so they may be able to avoid phishing attacks in the future.
A phishing attack refers specifically to an online scam use social engineering to coerce users in giving up personal information like social security numbers, bank account information and phone numbers. The most common means of phishing comes through spam emails. These emails are sent to hundreds or thousands of recipients and made to look like official correspondence from banks, service providers or even government agencies. Some include the threat of termination of service, while others will promise money or deals.
Spear phishing is an attack specifically targeting an individual or organization. By using information gleaned from other places, a hacker will put together an email that seems more legitimate because it will include information about you that a random person shouldn’t know.
This is usually how large-scale enterprises get hacked. They’re specifically targeted and employees are tricked into giving out their log in information, which opens the door for hackers to access the company’s network.
Anyone using email is at risk of a phishing scam. Trusting your spam filters helps to avoid many of the lazier phishing attempts, but you’ll also need to be wary of unsolicited emails asking for information you wouldn’t feel comfortable giving out to just anyone. Attachments, links, misspelled words and bad grammar are all signs that the email isn’t legitimate. In nearly every case, it’s better to contact a company by phone instead of replying to an email with personal information.
If you do fall for a phishing scam, you should immediately take action to change your passwords and monitor accounts closely for strange activity.
For help keeping your email secure and beefing up spam filters, contact Geek Rescue at 918-369-4335. We’ll help keep hackers out and your information secure.
August 28th, 2013

Recognizing that an account that you use often has been hacked is fairly easy. Recovering from a hack is much more difficult.
Matt Cutts, head of Google’s Webspam team, recently tackled this issue on his blog. As he notes, not only do you need to make sure the hacker no longer has access to any of your accounts, but you also need to safeguard for the future.
In the event that you have a hacked account, here’s what to do.
Take this opportunity to make passwords stronger using numbers, symbols and both upper and lowercase letters. If you’re changing multiple accounts, make sure you’ve secured your email address first. Otherwise, a criminal could have access to emails from other accounts informing you about your new passwords.
For Google accounts, and most email and social media accounts, you should be able to see when your account was last active. If you’re being told that someone accessed this account within the hour and it wasn’t you, you know there’s still a problem. You should also be able to find out where other users are logging in from.
For email accounts, a hacker may have set your address to forward to his. For other accounts, check to make sure your email address is still the one associated with the account.
- Consider two-factor authentication
This method is available for most accounts and requires both your log-in and password in addition to a code the website send you, usually over text message. This adds another layer of security and throws in an additional pass code that outsiders shouldn’t know.
Unfortunately, even if you’re careful you run a significant risk of a hack. Knowing how to recover quickly and re-secure your account is important so you don’t lose more than you have to.
For help with security at home or the office, contact Geek Rescue at 918-369-4335.
August 23rd, 2013
When spam email arrives in your inbox, it’s easy to ignore it, delete it and forget about it, right? Well, maybe not so easy for many of us.
As Chris Matyszczyk, of CNet, reports, a recent study found that about 30-percent of people knowingly, willingly opened an email that they knew, or at least strongly suspected, was spam. Why? Sometimes, the promise of something too good to be true is too good to pass up.
To make matters worse, about 9-percent of people willingly downloaded attachments included in the spam email. So, they thought it was spam, opened it anyway and downloaded the attachment. Sometimes, we make it too easy for the hackers.
Those hackers, however, don’t make it easy for users. It’s because of the social engineering they employ that it’s so enticing to open messages we know we shouldn’t. The most popular tactics are the promise of money, sex or a new friend.
This behavior is why having antivirus software installed on your computer isn’t enough to keep you fully secure. It is this human error that often causes viruses and malware to infect your PC and steal your data.
These tempting spam attacks extend beyond your email inbox, as well. You’ll see similar tactics used on social media and in text messages. You’ve likely already received a text from an unknown number informing you that you’ve won some money or are entitled to a free gift card. When those arrive on our smartphones, it’s easy to identify them as spam, but sometimes it’s much more difficult to delete them and move on.
If you’d like to improve the security on your email, or need to clean and fix a device that’s infected with malware, contact Geek Rescue at 918-369-4335. We understand spam is tricky, but we will fix whatever harm has been done.
August 9th, 2013
If you’ve taken every precaution to secure your companies network and email and have installed consistently updated anitvirus software on every device, there’s probably only a slim chance that any of your data is intercepted by an outside source, right? Actually, there’s still the matter of your employees to worry about.
IPSwitch recently published an ebook that illustrates all of the ways your employees are compromising security, which allows for the stealing of data. Usually, these employees are not intentionally putting data at risk. They’re simply trying to make data transfer easier for themselves or clients.
- Email Attachments- More than 84-percent of survey respondents admitted to sending confidential or classified information as an email attachment. 72-percent say they do so every week. Unless your company has specifically taken measures to protect attachments, all of the data sent this way is at risk.
- Using Personal Email– Rather than utilizing the secured, company email, about half of respondents use their personal email, which lacks adequate security measures, to send company data. They do so in order to send larger files, because it’s faster and more convenient, they can’t connect to work email outside the office and a variety of other reasons.
- Inadequate File Transfer Services- If they’re not sending valuable data via personal email or attachments, employees are using file transfer services, such as dropbox, or cloud services. Many times, the services they use are intended for consumers, not businesses. This compromises security and makes it impossible for IT to track how data is leaving their system.
- External Devices- Nearly 80-percent of respondents use a thumb drive or other external device to transfer, back-up or store data. The problem with having a physical device containing important data is that physical devices get lost or stolen. Almost a third of respondents say they’ve lost an external device containing sensitive business data. About half of those were not reported to the IT department, which means the possible compromise in security couldn’t be planned for.
This list is certainly not exhaustive. Due to a lack of education, or a desire to do what’s most convenient, employees often put your organization at risk. Having security measures in place is a great start, but more is needed to keep you secure. Call Geek Rescue at 918-369-4335 to find out what else needs to be done. We offer an audit of your organization that discovers bad practices and leaks in data. From top to bottom, in the physical and digital world, Geek Rescue keeps you and your business secure.
August 6th, 2013
There are about 12-million people who are the victims of identity theft each year. In the US alone, identity theft costs about $18-billion. What can you do to avoid having your identity stolen?
As Abigail Wang, of PC Mag, points out, the key to staying safe is taking precautions offline, as well as online.
Shredding documents, especially mail like bank or credit card statements, that contain personal identifiable information is vital in keeping your identity safe. Even address labels that include your name could be harmful. Before you throw out junk mail, be sure to shred it. When mailing checks, drop them off at the post-office instead of leaving them for the mailman.
Online, it gets trickier to make sure you’re safe. Installing robust antivirus software is a necessary precaution and goes a long way to protect your security. You’ll need to keep that software up to date at all times.
In your email, trust your spam filter. If an email looks suspicious, don’t click any links contained in it and avoid opening at all if possible. Deleting old emails containing account information is also a good idea in case a hacker gains access to your inbox.
On social media, use privacy controls so that people you don’t know can’t see your personal information. It’s amazing how much someone with some expertise can do with just your birthday and hometown.
To keep your email and computer safe, contact Geek Rescue at 918-369-4335. We install state of the art security software that locks out hackers. Every three seconds, someone’s identity is stolen. Don’t let yourself be a victim.
July 26th, 2013

Many people think they don’t need to worry about criminals hacking into their email accounts because there is nothing of value or interest in their inbox. Most likely, that’s not true. Fahmida Y. Rashid, of PC Magazine, reports that a tool from the University of Illinois- Chicago puts a value on your email to give you an idea of why someone might want to access it.
Cloudsweeper puts itself into the mind of a cybercriminal and scans the emails saved in your inbox to find potential value. Hackers are looking for account information, passwords and even other sites associated with your email address. They can use password resets to change your existing passwords, then read the email the site sends to you to get the new one. That means that any email you haven’t deleted from a site you have an account at could be dangerous to you in the case of a hack.
The service isn’t perfect. It pops up with false positives if you happen to keep emails from sites like Facebook or Amazon but don’t actually have an account there. Still, it lets you see what messages you should consider deleting before they fall into the wrong hands.
To fully protect your email, call Geek Rescue at 918-369-4335. Don’t let your personal information or account information get out. Geek Rescue keeps you protected with the latest security software and IT services.
July 24th, 2013

We’ve all been conditioned to be afraid of viruses on our computer and for good reason. Viruses slow down performance, cause crashes and cost you money. Drew Pindle recently addressed this topic for Digital Trends and revealed why it’s a good idea to learn some tell-tale signs that you may have a virus hiding on your computer, how to get rid of it and how to avoid getting it in the first place.
One of the most obvious signs that you’ve got a virus is pop-ups. To be fair, even with a well-configured, up-to-date web browser, you could still see a couple pop-ups now and then. This doesn’t necessarily suggest you’ve got a virus. However, if you’re seeing pop-ups when you aren’t even using your browser, a virus is the likeliest reason. There are a number of malware removal tools available to help you in this case. For a thorough cleaning, call Geek Rescue and they’ll remove the malware from your computer to stop the annoying pop-ups.
Another sign of a virus is learning that your email or social media account sent out messages without your knowledge. Many of us have been the unfortunate victim of a hijacked, or hacked, email account. There are few things that make you feel as frustrated and helpless as learning your email spammed your entire address book. Viruses often do this as a way to spread to other computers. If you notice your email or social media account has been hijacked, change your passwords and scan for viruses. Consult the experts at Geek Rescue to help keep your email safe and eradicate harmful viruses.
This is one of the scariest virus signs. Ransomware does exactly what the name suggests. It holds your computer hostage and asks for payment. Usually, a message takes over your screen, which can even include an official looking government seal, informing you that your computer has been locked down until you pay some sort of “fine”. If this happens to you, don’t reveal any payment information because this is a scam. Unfortunately, it’s incredibly difficult to recover from this type of takeover. You’ll need a rescue disk, or the professionals at Geek Rescue. They have experience with ransomware and get you back on track quickly.
If you find your computer has grown sluggish and suddenly freezes or crashes often, that’s another sign of a likely virus. Your computer could deteriorate over time on its own, but if it goes from being fine one day to almost unusable the next, a virus is probably the culprit. Most likely, this virus can be spotted by opening task manager and looking for any suspicious programs that are running.
You may find that task manager, or other essential programs, won’t open on your computer. That’s probably because a virus is blocking them. They could even be blocking your antivirus software, which makes it a difficult fix. Bring your computer to Geek Rescue to get your computer cleaned and protected against future infections.
If you’ve made it this far into the article without any of these symptoms sounding familiar, you may be thinking your computer is completely clean. You may be right, but it’s just as likely that you have a particularly well-crafted virus hiding from you. The most effective and dangerous viruses don’t announce their presence. Instead, they infect your computer without noticeably affecting anything. In fact, some viruses have even been programmed to delete other malware to keep antivirus software from detecting an infection. To make sure your computer is infection-free and you’re safe, bring your computer to Geek Rescue to get your computer cleaned and protected against future viruses. Come by or call us at 918-369-4335.
July 19th, 2013

Despite your best efforts, it’s fairly likely you’ll click on a bad link or open an email you shouldn’t have at some point. When that happens and you get an email from a contact informing you that your address has been spamming everyone with malicious links, you’ll need to take action. Adam Levin has some tips on how you come back from an email hacking at Huffington Post.
- Change Your Passwords– It’s possible that whoever gained access to your email already changed your password and locked you out. If not, change to a stronger password to lock them out. Don’t limit the change to just the hacked email account either. Take this opportunity to make all of your important online accounts more secure. You have to assume every account associated with your email could have been compromised. You may want to do this on a different device than you usually access your email in case malware is allowing the hacker to steal your passwords.
- Report The Hack– Your email provider has a plan in place for compromised attacks. They will help you through this process. It’s also a good idea to tell any business you have an account with associated with the hacked email, especially a bank. And, of course, warn everyone in your contacts list to be wary of emails from your account.
- Scan With An Antivirus Program– As I mentioned, the hacker may have gotten your password initially thanks to a monitoring malware on your computer. Without checking for malicious programs, you may open yourself up to hacks of other accounts.
- Review Email Settings– The cyber criminal may have set up a forward email to continue monitoring your activity and stealing information. Be sure to delete those and make sure everything else is the way you want it.
Even after taking these necessary steps, you’ll want to closely monitor your bank accounts and credit score. Unfortunately, knowing your email has been hacked doesn’t mean you know all of the personal information the hacker gained access to. To keep your computer, email and identifiable information safe online, call Geek Rescue ta 918-369-4335. We use the latest software to keep your system safe from intelligent, and ever-evolving, attacks.
July 17th, 2013
Have you heard of a Distributed Spam Distraction or DSD? It refers to the use of a flood of spam emails overwhelming your inbox to distract you from important emails detailing a cybercriminals real actions. John P. Mello details the dangers of a DSD attack for CIO.
Though still fairly rare, there’s been a spike in the number of DSD occurrences since the beginning of the year. The attack can last up to 24 hours and send a deluge of 60-thousand messages to your inbox. The spam is difficult to filter since it contains no malicious links or malware. The criminals make messages as simple as possible because their purpose is just to distract you.
If you experience a DSD attack, someone has obtained not only your specific email address, but also account information and passwords for an important site. While you’re sorting through a ridiculous amount of emails, usually filled with random quotes from books, criminals make changes to your online accounts, possibly transferring money or making purchases. Since these actions automatically send an email to your inbox, the spam is used to cover them and keep you unaware.
It’s important to change passwords and stay diligent in combing through spam emails when experience a DSD attack. Contact Geek Rescue at 918-369-4335 immediately for help. They help you deal with the attack and protect you from future attempts to steal your data.
July 12th, 2013

To many people, being invisible and undetectable on the internet is only necessary for criminals who are partaking in illegal activities. Those people overlook how easy it is for websites and other users to monitor your activity and steal your information. Fortunately, there are plenty of ways to stay safe by going invisible. Chris Gayomali touched on a handful of your options in his recent article for The Week.
Masking your IP address makes it more difficult to track your online activity, which is a particularly valuable skill considering the recent developments with the NSA. Your IP, or internet protocol, address is a set of numbers assigned to your device. Computers, phones, even printers, all have an IP address. To mask your IP, your connection to the internet is rerouted through other machines, which makes it hard to pin down where you actually are. There are programs readily available for download to help with this task, although some websites may not support your masked IP experience. Geek Rescue will outfit your computer with top-of-the-line software to mask your IP and keep you safer online.
Have you ever heard of a VPN? It stands for Virtual Private Network and they supply encrypted tunnels to keep your online activity secure. Again, there are plenty of downloadable tools to help you set-up your own VPN. They come in handy when using free WiFi, which are by definition unsecure networks and attract shady characters. To set up your own VPN, call Geek Rescue or stop by. They’ll have you surfing securely in no time.
You may not be using your email for any illegal activity, but that doesn’t mean you want anyone to have access to your message content. Addresses, phone numbers, bank account numbers and social security numbers are routinely included in emails. Encryption services are readily available and many don’t even require registration. Geek Rescue has the email solutions you need to ensure that no outside sources have access to your private messages.
Google, Microsoft and Yahoo have all been accused of sending information to the government. What do you do if you don’t records of your searches forward to official agencies? A little research can help you discover a new search engine that promises not to track or store records of your searches. Predictably, traffic on these search engines has risen steadily in the past few weeks.
Finally, if the search giants’ sites aren’t safe, neither are their chat clients. Encrypted chat services are often as easy as adding a plug-in to your browser. It may not be quite as convenient as Gchat, but you can be sure that no one else is reading your conversation.
For more information on how to surf safely and keep your computer and data private and secure, talk to the experts at Geek Rescue today. Give us a call at 918-369-4335.