September 20th, 2013

Malware infects your computer and affects its performance. Or is that a computer virus? Are they the same thing?
Lincoln Spector, of PC World, writes that the difference between malware and virus is ambiguous at best. Technically, a virus is a form of malware. That’s not always the way it’s used today, however.
Not only is a virus a form of malware, but trojans, worms and rootkits are also. Malware is classified as a piece of code that infects your computer and performs actions independent of the user, which is you. To simplify, it’s something that has found a way onto your computer, by way of a download, upload, or a number of other ways, and is doing things without your knowledge, like monitoring your activity, harvesting data or spamming your address book.
A virus falls into the malware category because it infects your computer and is capable of performing independent actions. A virus infects an existing file and corrupts it. But, there aren’t many viruses around today because they’re seen as inefficient by cyber criminals.
The reason the terms malware and virus have become interchangeable is because computers and malicious programs existed before ‘malware’ became a term. So, whenever anyone spotted one of these malicious programs and in the 1980’s and 90’s, they referred to them as a virus. That’s been a hard habit to break even as we now understand the differences between unique forms of malware.
While your security software is called ‘antivirus’, it likely protects you from a variety of malware. To simplify security, call Geek Rescue at 918-369-4335. We understand malware and viruses and, more importantly, know how to keep you safe and secure.
September 19th, 2013

Regardless of how many safeguards you have in place, your company’s data is never completely secure. Security tools like antivirus software and firewalls are helpful, but they can’t guarantee your safety.
Sam Narisi, of IT Manager Daily, points out that data breaches and cyber attacks create a number of negative results beyond just the loss of data. Employee and system downtime, money lost, damage to a brand’s credibility and compliance failure are all possible when your security is compromised.
One step towards improving security is to understand how your current security infrastructure is being infiltrated. Here’s some of the latest hacker tactics.
Everyone is aware of the dangers online so most companies focus their security to protect them on that front. However, 25-percent of companies victimized by a malware attack say it originated from an individual’s USB device. To accomplish this, cyber criminals send out complimentary USB devices, which are disguised as promotional material for a company and infected with malware. They also leave USB devices sitting in coffee shops, bars, restaurants or on the street. Eventually, someone picks it up and tries to use it.
An employee working at the office on your secure network is well protected. That employee may take his laptop or smartphone elsewhere to work, however. Especially if connected to a free WiFi network, that employee would now be vulnerable. Hackers could gain access to anything stored on their device, and then gain access to the company’s network when they return to work.
- Holes in Security Software
Even with antivirus software in place, you’re vulnerable. 40-percent of companies who have experienced a malware attack say the threat slipped through security software already in place. That software has a difficult time keeping up with new malware, even when it is regularly updated. Since hackers have such a deep understanding of how antivirus programs work, they are developing malware that stays undetected.
Having the right tools in place is still a good place to start to avoid a malware infection. Proper training for employees is another necessary precaution. If you still find that your network has been infiltrated, call Geek Rescue at 918-369-4335. We will disable the threat and also keep you better protected for the future.
September 19th, 2013

Everyone is interested in the silver bullet that will magically make them completely secure and afe from any cyber threat. It doesn’t exist, but as Thorin Klosowski points out at Lifehacker, there are a number of ways to become more secure within minutes.
By far the simplest and quickest way to improve security is to enable 2 factor authentication on your online accounts. With this more secure type of log-in, you’ll be prompted for your password, but you won’t be given access to your account until you’re given a second authentication method. In many cases, you’ll be texted or called with a code to enter to prove that you are who you say you are. Once you’ve gone through this process, a hacker would need to using your computer, or have your smartphone to gain access to your account.
A password manager can be added to practically any browser and will automatically log you into accounts that have been added to it. This actually sounds less secure, but the password manager locks away all your passwords and encrypts them so they’re safe. You’ll only need to remember one master password to use the password manager. Many managers will even generate a strong, random password for each site you wish to use with it, so the only way to log in to those accounts is by having access to the password manager.
Email encryption has some headaches associated with it. Most notably, encrypted emails require a key to read, so whoever you’re sending a message to will need the key. But sending them the key over email defeats the purpose of encryption. You probably don’t need to encrypt every email you send, but messages containing information like bank accounts, social security numbers or even contact information are good candidates for encryption. Just be sure to send the encryption key through text, or in person.
Backing up your files is always a good idea, but, just like email, it’s important to encrypt files containing potentially valuable data. There are a number of services that offer encrypted back ups, but one obstacle is that usually these encrypted files won’t be available to you on another machine. That means you won’t be able to access them from your smartphone or at work.
These steps will improve your online security, but nothing is unhackable. The idea is to make it as difficult as possible for anyone to access your data and accounts. Geek Rescue specializes in improving your cyber security to keep your information safe and your devices free from malware. Give us a call at 918-369-4335 to find out how to strengthen your security.
September 18th, 2013

The focus of data breaches is usually on the company who was breached. Articles detail how to better secure your company’s data and how to recover if your company gets hacked, but what about the users whose personal information is now in the hands of criminals?
If you are informed by a company you have an account with that your data has been compromised, Andy O’Donnell of About has some advice for what to do next.
The absolute first thing to do is change the password on the compromised account. This isn’t a futile effort. Most likely, your log-in information is just one of thousands or millions of log-ins stolen. There’s a good chance that the hackers haven’t even been able to try it yet. So, change that password immediately and you could save yourself a lot of trouble. To be safe, take this opportunity to change the other passwords on your most used accounts. Passwords should be changed periodically anyway, but if a knowledgeable criminal has your email address and other information, it’s possible they’ve hacked into other accounts.
- Contact Your Bank And Credit Card Companies
Even if your bank was the company who contacted you about the breach, you’ll want to make sure there’s a fraud alert on your accounts. This way, any suspicious activity will be immediately noticed and you won’t end up with thousands of dollars missing. You’ll probably also want to get new credit and debit cards with new numbers. Credit card information is often the goal of any data breach, so if there’s any way the compromised company had your card number on file, be proactive and get a new card.
- Ask About Free Identity Theft Prevention Services
It has become common practice for a breached company to offer this service to their affected customers. But, you may have to ask to get the offer. Or, asking may cause them to offer it to you even if they weren’t planning to originally.
- Request A Freeze On Your Credit Report
This isn’t for everyone as their are positives and negatives to a security freeze. Do your research before requesting one. The reason it may be useful is that criminals who have access to your personal information will likely attempt to open a line of credit with it in your name. Irreparable harm could be done to your credit score if left unchecked.
Should you learn that your valuable data has been stolen from a company you do business with, you’ll want to act quickly to avoid as much damage as possible. You can’t get the data back, but you can make it significantly less valuable and prevent it from hurting you.
Geek Rescue helps business stay more secure in order to avoid these data breaches. We also help keep your home computer and network secure, so your personal information isn’t stolen directly from you. To find out how Geek Rescue helps your home and business, give us a call at 918-369-4335.
September 18th, 2013

A Denial-of-Service attack, or DoS, refers to an attempt by a cyber criminal to interrupt your ability to connect to users. These attacks are launched against websites, networks and apps to disable them, usually by overloading the target with communication requests. In other words, the hackers force the website or network to shut down due to an excessive amount of traffic.
Bob Gorski, of PivotPoint Security, notes that about 65-percent of organizations have experienced three DoS attacks in the past year. The assumption is that hackers target large enterprises like banks and government agencies. However, small business owners need to be prepared for attacks also because their lack of security is attractive to criminals and they also possess valuable data.
The motivation behind a DoS attack can be as simple as an individual being upset at a company. That individual then launches the attack to shut down service and cost that company money. It can also be more complex than that.
DoS attacks have been known to be fronts, or distractions, from more sinister actions. While your security team works to get your website or network back online during an attack, hackers are installing malicious software or harvesting your data.
In another scheme, hackers disabled a site with a DoS attack, then were able to hijack the company;s social media account and redirect users to a phishing site. Users have log-ins and personal information stolen and blame the company.
Firewalls and antivirus software doesn’t protect you from a DoS attack. The best way to be prepared for one is to test. Load testing puts a strain on your website or network to find out if it can handle a DoS attack. This can cause the target to go down, which is why it’s best to run these tests at off-times but when an administrator is available to quickly get your website or network back up.
Geek Rescue helps you prepare for cyber attacks and uses the latest security solutions to safeguard your website and network. Give us a call at 918-369-4335 before an attack causes your business to grind to a halt.
September 17th, 2013

The iPhone 5s will be released soon, which has security experts scrambling to figure out what flaws could be exploited by hackers. Because the new iPhone, and even its new operating systems, iOS7, haven’t been officially released, Matthew J. Schwartz made some educated guesses about possible security concerns at Information Week.
New operating systems usually make sure to shore up any security holes that previous versions may have had. In the iPhone’s case, the previous operating system was considered “a freaking vault” according to one security researcher. The concern then, is that any new operating system will have flaws of its own that are just waiting to be discovered.
A new processor also suggests new flaws to be exploited. But, the new processor promises to make previous exploits obsolete and reportedly makes jailbreaking, or gaining root access to the device through bugs, much more difficult.
Multiple security experts suggest the fingerprint scanner, or Touch ID, will draw most hackers attention initially. There have already been multiple suggestions about how to break through the new iPhone’s security measure.
One tactic, dubbed a “phish finger”, would be to take a finger print from the touch screen and use it to fool the fingerprint scanner. New technology is supposed to make it difficult to fool the scanner without an actual finger, but it can still be done.
Fingerprints of the iPhone’s owner are encrypted and stored on the device, so one theory is that these fingerprints could then be stolen and used to hack into the device. However, the way the fingerprints are stored makes them only recognizable to the iPhone’s processor, which means they can’t be exported to another device.
Touch ID isn’t the only security measure on the iPhone 5s. A password is still in place as well and is required in some situations.
There are certainly some security upgrades on the new iPhone, but there appears to be some potential vulnerabilities as well. In the coming days, more of these vulnerabilities will likely be revealed as more hackers and security experts have hands-on time with the iPhone 5s.
If you need additional security on your mobile device, be it a new or old iPhone, Android or other, bring it to Geek Rescue. We improve security, get rid of malware and fix broken hardware. Come by or call us at 918-369-4335.
.
September 17th, 2013

If you’ve used Twitter, you’ve likely encountered Twitter spam. There are unfortunately a large number of profiles whose sole purpose is to send out messages with URLs that are phishing sites or infect your machines with malware. Twitter has taken steps to rid their users of this spam nuisance, but spammers now have new tactics that are more difficult to deal with.
Kit Eaton, of Fast Company, reports that the latest spam technique involves Twitter’s lists. Twitter overcame their initial spam issue by adding a “Report Spam” button for users to use when they encountered an obviously malicious tweet or profile. Overcoming list spam is more complicated.
When your Twitter profile is added to a list by another user, you receive a notification. Lately, users have been seeing list add notifications from spammers masquerading as reputable companies. Accounts trading on the names of Paypal or Facebook appear to have added your Twitter handle to a new list. The idea behind this scheme is that users will have questions about this action and want to know more.
Naturally, you’ll click on the name of the account that’s just added you and you’ll arrive at a barren Twitter profile. No profile picture, only a few tweets sent and almost no followers. Their bio will contain a URL, however. Don’t click it. The urge might be to follow the link and find out what this strange Twitter profile is all about, but the URL points to a malicious website. This could be a phishing scam or a website designed to infect your device with malware.
Twitter has yet to announce a plan to deal with this latest spam threat. You can avoid any problems, however, by being suspicious. Understand what a spam Twitter profile looks like and don’t click any links in their bio or tweets.
If you find that you computer or mobile device has been infected with malware, bring it to Geek Rescue. We rid any device of viruses and malware. Come by or call us at 918-369-4335.
September 12th, 2013
A new form of malware attack on Android phones has security experts on the look-out. This form of scareware infects your computer through a phishing email and malicious link.
Chris Brook, of ThreatPost, reports that the emails will appear to be from the United States Postal Service.
The message informs you that the USPS was unable to deliver your package because the postal code contains an error. You’re then prompted to print a label. When you follow the “Print The Label” link included in the email, a malicious Android Package File, or .apk, is downloaded to your device.
This particular scam seems poorly constructed. After all, most of us know when we’ve sent a package recently and understand that printing a label for a package that isn’t in our possession wouldn’t do much good. However, there are plenty of users who will click the link to try to gain more information, even if they haven’t sent a package in months. Hackers play on our curiosity and even thin attacks like this one will claim victims.
This form of malware has been used before. Security experts note that a previous scam using it in a scam that asks users to pay a subscription fee to keep their devices clear of malware. What’s noteworthy is the way the malware is being distributed. Cyber criminals are adjusting to the number of users who access their email on their Android devices and are attempting to exploit that fact.
This malware is reportedly even capable of intercepting both incoming and outgoing calls. It also is capable of changing file names to look more innocent. Instead of a suspicious .apk file, it will appear as a .zip file with a tantalizing name like vacationphotos.zip.
Android users should go into the settings on their device and disable the option to “allow installation of apps from unknown sources”. Users will also be able to enable a “Verify Apps” option, which will warn them before any potentially malicious app is downloaded.
These two options help keep your device safe, but you’ll also want dedicated security apps as well. To upgrade the security on any of your devices, or to rid them of existing infections, come by or contact Geek Rescue at 918-369-4335.
September 11th, 2013

Many small business owners believe that they won’t be the target of a cyber attack simply because there are larger companies that present more value to hackers. However, this belief leads to more relaxed security protocols, which makes small businesses an attractive target because of their ease of access.
Susan Solovic posted on the AT&T Small Business blog how to immediately improve your company’s security without having extensive expertise.
As with any account, you need to protect your business by having each employee log-in with a secure password. This password should be long, have upper and lower case letters and symbols and numbers and be changed often.
It’s a basic step that pays big dividends. Don’t make it easy for a criminal to steal your information or infiltrate your network. When you’re not sitting at your computer, sign out. This erases the possibility that someone in the area could walk by and immediately access valuable data. This is especially important for mobile devices.
There’s a reason your antivirus software requires regular updates. Hackers are constantly changing tactics and using new techniques. Each update is an attempt to stay ahead of the curve. So, when any of your regularly used applications prompts you to update, do it.
Nothing keeps you 100-percent secure. Even if you are able to avoid a cyber attack, natural disasters could still wipe out data. Regularly backing up vital data is important in order to avoid a catastrophe. Should any of your files be lost or corrupted, you’ll have back-ups to replace them quickly without suffering any down time.
Each employee and each position at your company is different. Some will require different access to different applications. Think of it like a government security clearance. There are different levels depending on your pay grade. For your business, give employees the access necessary for them to do their job, but no more. This way, if their account is compromised, you won’t be allowing access to your entire network.
Keeping your business secure is an important and time consuming job. For help, contact Geek Rescue at 918-369-4335. We offer data storage and back-up, security solutions and more.
September 11th, 2013
Would you call your passwords to the various accounts you have online secure? It depends on how many characters your password is, if you use upper and lower case letters, symbols and numbers, if you use full words, recognizable names or places from your life and whether you reuse passwords on multiple sites.
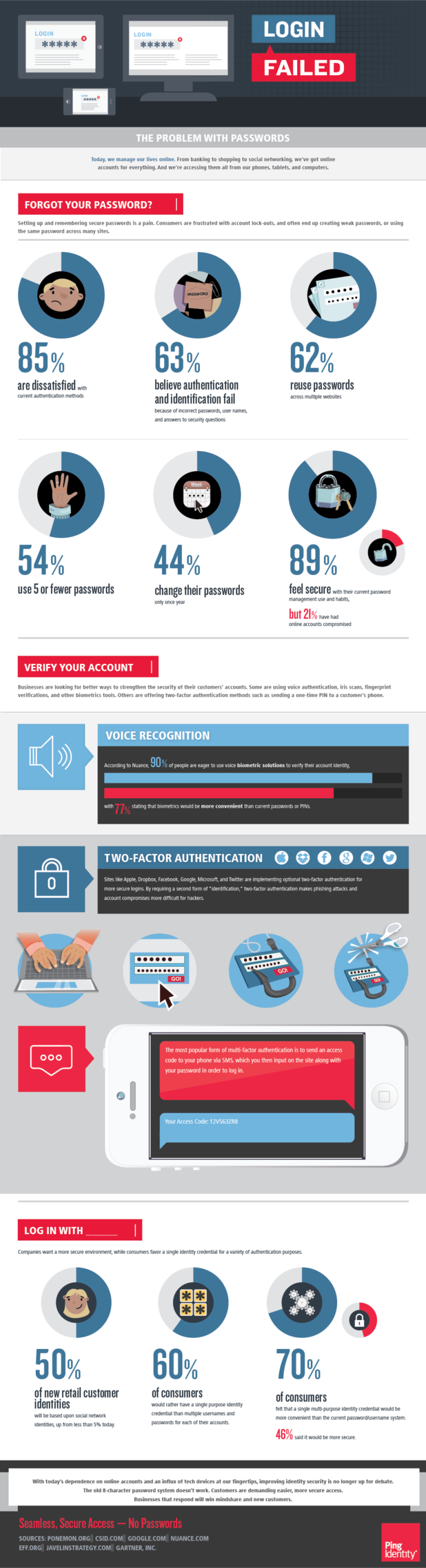
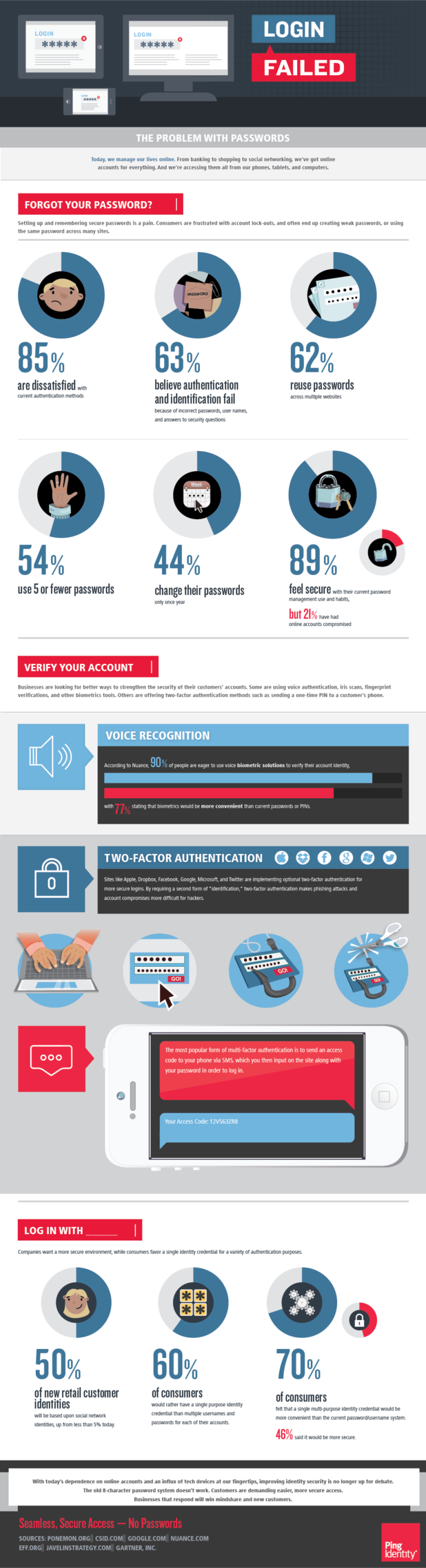
Ping Identity’s Christine Bevilacqua published a blog along with the included infographic that speaks to the problem with password security.
Many of us have experienced a compromised online account and a broken password is often to blame. There is software readily available that is capable of breaking even incredibly long passwords. Sometimes, the strength of your password isn’t even the issue.
In the case of the latest attack on the New York Times, a spear phishing scam resulted in an employee giving out their password. Cyber criminals have become increasing intelligent about creating ways to hack into your accounts.
If you aren’t scammed into giving out your password outright, you may be guilty of clicking a link or downloading an attachment you shouldn’t have. This could infect your computer with malware capable of monitoring your activity, stealing passwords and infiltrating your accounts.
Some online accounts are moving to require a log-in with social media accounts, but what protects your social media accounts? A password does.
One of the latest innovations on the new iPhone is the use of biometrics. In order to unlock the phone, users will use their fingerprint. This seems like a foolproof plan. Afterall, no one will be able to hack into your phone unless they have your fingerprint. However, the problem becomes the unreliability of biometrics. For example, what happens if an error occurs and your phone won’t recognize your fingerprint? For most similar systems, the fall back is simple password protection, which brings us back to square one in terms of security.
The key to avoiding a hacker cracking your password is to practice safe surfing techniques and to have the latest security software in place.
To make any of your devices more secure, contact Geek Rescue at 918-369-4335.